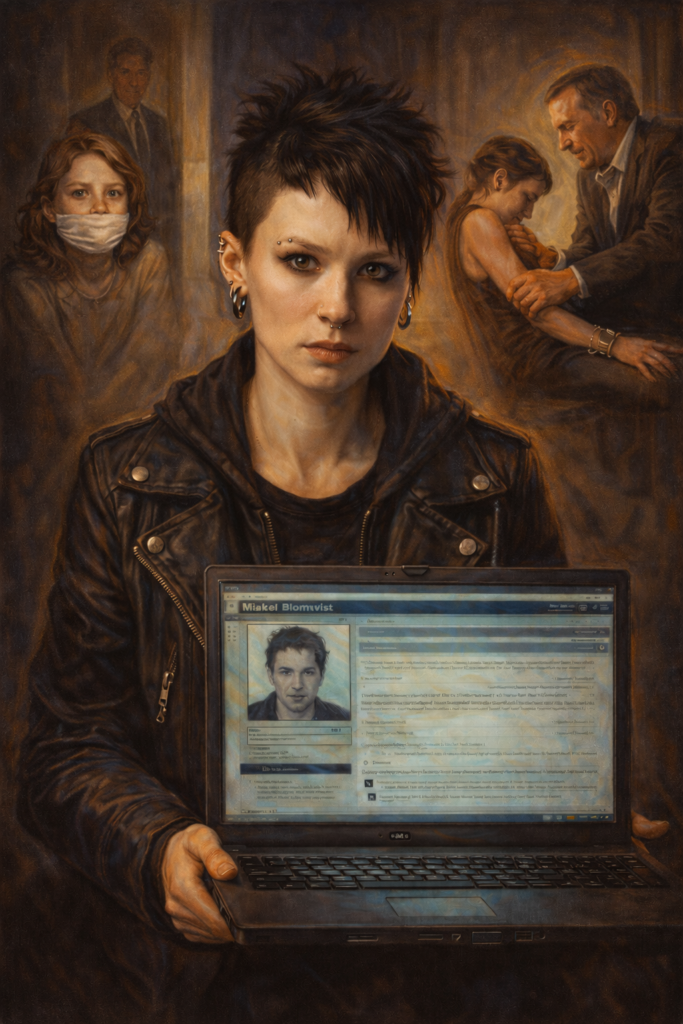
This The Girl with the Dragon Tattoo 2011 character study explores Lisbeth Salander’s psychology through one core idea: for her, trust is not a warm feeling but a designed system built from boundaries, verification, and leverage. Understanding that system offers readers a powerful lens for their own relationships and self‑protection.
- Lisbeth treats trust as a constructed system of rules, checks, and safeguards.
- Her trauma and institutional betrayal reshape connection into a calculated risk assessment.
- Viewers can adapt her boundary-setting without copying her illegal or extreme behaviors.
Trust As Something You Build, Not Something You Wait For
Most of us are taught to think of trust as a feeling: you either sense someone is safe, or you do not. Lisbeth Salander lives in a different world. In David Fincher’s 2011 film, she treats trust like a security protocol you design, test, and update. According to Rogerebert, this analysis holds true.
Instead of waiting to “feel” safe again after hurt or betrayal, Lisbeth shows a harsher but empowering path: you can architect how people enter your life, what they can access, and how quickly.
This analysis follows Lisbeth through The Girl with the Dragon Tattoo (2011) to unpack how trauma, boundaries, and verification shape her worldview—and then turns those dynamics into practical, ethical strategies for real life.
Who Lisbeth Is In The 2011 Film
In the film, Lisbeth Salander is hired as a researcher and hacker to investigate journalist Mikael Blomkvist before he is brought into the Vanger family cold case. She is under state guardianship, branded legally incompetent, and controlled by institutions that have repeatedly failed and abused her.
We meet her as:
- A world-class hacker working semi-clandestinely.
- A ward of the state under a new guardian who sexually abuses her.
- An outsider whose appearance and behavior mark her as dangerous and “other” to those in power.
The story places her near constant danger—sexual violence, legal coercion, and corporate corruption. Institutions that should protect (social services, guardianship, psychiatry) are instead weapons used against her. In that environment, naive trust is not just foolish; it is life-threatening.
Lisbeth’s Psychological Landscape
Lisbeth’s distrust is not random attitude; it is a logical outcome of her history.
Trauma And Institutional Betrayal
As a child she witnessed and retaliated against her father’s violence, then was institutionalized. Over time, psychologists, social workers, and guardians framed her as the problem. Her rage at abuse was pathologized; the abusers were protected.
This is institutional betrayal: systems that claim to safeguard the vulnerable instead silence or punish them. Psychologically, this sets up a deep rule: people with power are more dangerous than strangers. Paperwork, titles, and official roles are not markers of safety; they are red flags.
Neurodivergent‑Coded Traits And Hypervigilance
Without pinning on a diagnosis, the film codes her with:
- Intense focus and pattern recognition.
- Social differences: flat affect, minimal small talk, blunt communication.
- Sensory and privacy boundaries around touch, space, and information.
Layered over trauma, these traits feed hypervigilance. She scans for threats through data instead of facial expressions. Where others lean on intuition, she leans on evidence. Review: The Girl with the Dragon Tattoo (2011) The Girl With The Dragon Tattoo: A Masterclass in Meticulous Character Study
Her starting stance is not “trust until proven otherwise” but “assume threat until thoroughly disproven—and even then, keep leverage.”
Trust As Lisbeth’s Operating System
Lisbeth does not experience trust as an emotion first and a decision second. She inverts that sequence: she builds a system, runs tests, and only then allows emotion to enter. Several key behaviors show her “trust operating system.”
Surveillance As Risk Assessment
When she is first hired to look into Blomkvist, her job technically ends after she submits her report. But she keeps watching him: she hacks his emails, monitors his investigation, and tracks his moves.
Before she ever meets him, she:
- Knows his legal trouble and moral stance on the Wennerström case.
- Evaluates his patterns of persistence and moral outrage.
- Sees that he is willing to be humiliated publicly to pursue truth.
Surveillance, for her, is step one: gather data at a distance where you cannot be hurt.
Information As Armor And Leverage
Lisbeth rarely walks into a room without some kind of advantage. With her abusive guardian, she records the assault and later uses the video to regain control of her finances and body.
A harsh equation forms in her mind:
- People in power will exploit you if they can.
- Evidence is the only language they respect.
- Therefore, never engage without leverage.
Within her world this is rational self-defense. Trust, in this system, is not giving someone the benefit of the doubt; it is giving them temporary access under strict conditions, backed by proof of what they have done.
Controlled Disclosure
Lisbeth shares almost nothing about herself voluntarily. Names, addresses, history—these are all need-to-know. Even with Blomkvist, the information flows when it serves a function (investigating the case) rather than when emotion demands intimacy.
Her rule: you earn each layer of my story through consistent behavior, not through emotional closeness alone.
The Lisbeth–Blomkvist Trust Arc
The film shows how her system reacts to Blomkvist and how her distrust is negotiated over time.
Stage 1: Observation From A Distance
Before they meet, she has already built a detailed psychological profile of him. When he tracks her down to ask about the background report, she is surprised—but not unprepared.
Key mechanic: He respects her competence. He does not treat her like a tool; he treats her as an expert and equal. That is the first crack in her default “assume threat” stance.
Stage 2: Test Collaboration
When he asks her to join the Vanger investigation, she does not instantly agree. She tests him practically: she shows up, begins working, and observes how he handles her bluntness, speed, and unconventional methods.
Moments that deepen trust:
- He gives her full access to the case materials without micromanaging.
- He adapts to her working style instead of forcing her into his.
- He accepts her breaking into archives as part of her toolkit.
Each of these is a passed test: Will you try to control me? Will you shame me? Will you slow me down to reassure yourself?
Stage 3: Physical And Emotional Proximity
Their sexual encounter is matter-of-fact on her end. She initiates, sets the tone, and treats sex as one more domain where she maintains control. Trust deepens not because of sex, but because of subsequent behavior:
- He treats the encounter without judgment or entitlement.
- He does not demand explanations for her scars or history.
- He continues to collaborate with respect.
For Lisbeth, consistency after vulnerability is the proof she needs. Blomkvist does not weaponize what he knows about her or what they share.
Stage 4: Crisis And Loyalty
When the investigation turns physically dangerous, she repeatedly chooses to protect him, using her skills to save his life and continuing to help even when she could walk away.
By the end, she takes a huge emotional risk on his behalf in the financial revenge subplot. When that risk is not reciprocated in the way she expects, you can almost feel her internal system rewriting its rules again. Trust was possible; it was also fragile.
Boundaries, Control, And Consent
Lisbeth’s life is a battlefield over control of her body, money, and freedom. Her boundaries are survival tools and sometimes relational barriers.
Healthy elements we can learn from:
- Clear control over access: She decides who enters her apartment, who touches her, and on what terms.
- Explicit consent in her own way: When she initiates intimacy, it is direct and unambiguous.
- Refusal to normalize abuse: With her guardian, she documents and counters his violence.
Unhealthy or risky elements:
- Isolation: Keeping everyone at arm’s length denies her access to support.
- All-or-nothing trust: People are either fully locked out or suddenly given huge importance.
- Reliance on leverage: Building relationships around secret evidence and blackmail is not sustainable.
Her boundaries are forged in crisis. They protect her, but they also cost her connection.
Table: Lisbeth’s Trust Behaviors – Myth Vs. Real-Life Application
|
Film Pattern / “Myth” |
What It Represents Psychologically |
Ethical Real-Life Adaptation |
|---|---|---|
|
Hacking and surveillance |
Hypervigilance, need for information before closeness |
Ask questions, take time, check patterns of behavior |
|
Recording and blackmailing her abuser |
Regaining power after extreme institutional betrayal |
Document abuse, seek legal help and trusted advocates |
|
Extreme privacy and secrecy |
Fear of exploitation, protecting vulnerable self |
Share selectively, build circles of graduated disclosure |
|
Sudden intense loyalty to Blomkvist |
Hunger for safe connection once basic trust is earned |
Allow gradual closeness, stay aware of your own pacing |
|
Violent revenge |
Fantasies of justice when systems fail |
Channel anger into advocacy, boundaries, and legal routes |
From Fiction To Practice: Building Your Own Trust System
Lisbeth’s methods are often illegal and dangerous, but the psychological logic underneath them can be translated into ethical, practical tools.
1. Move From Vibes To Criteria
Instead of “I just trust them,” try questions like:
- How do they respond to my boundaries?
- Do their actions match their words over time?
- How do they behave when they are frustrated or told no?
This is Lisbeth’s data-driven instinct in humane form: trust as observable pattern, not wishful thinking.
2. Use Graduated Disclosure
Think in layers, not all-or-nothing. Start by sharing low-stakes information. If someone handles that with respect and consistency, share a bit more.
You are doing what Lisbeth does with her files—releasing access bit by bit—but through conversation and emotional sharing instead of hacking.
3. Build Boundaries Before You Need Them
Decide in advance:
- What behavior is an automatic no for you.
- How you will respond when a line is crossed.
- Who you can call if you feel unsafe.
Pre-made scripts (“I am not comfortable with that,” “I need to slow this down”) are a softer cousin of Lisbeth’s contingency plans.
4. Separate Safety From Punishment
Lisbeth’s world blurs protection and revenge. In real life, your priority is safety, not payback.
Ethical translations include:
- Documenting concerning behavior (screenshots, notes).
- Reaching out to trusted friends, therapists, or hotlines.
- Using formal channels when possible: HR, legal aid, advocacy groups.
You can honor the part of you that wants justice without replicating her vigilantism.
Limitations And Cautions
It is tempting to romanticize Lisbeth as the ultimate survivor who needs no one. Underneath the leather and hacking is a person who cares deeply and is repeatedly wounded when institutions and people confirm her worst expectations.
Important cautions:
- Do not copy her illegal strategies. Hacking, blackmail, and violence are crimes and also keep her trapped in cycles of danger.
- Hypervigilance has a cost. Constant monitoring can exhaust your nervous system and block intimacy.
- Total self-reliance is a trauma story, not a goal. Lisbeth’s independence is impressive, but it is also lonely.
Her coping patterns make sense within a context of lifelong betrayal. They are adaptations, not blueprints.
Frequently Asked Questions
How does Lisbeth Salander define trust as a security system?
Lisbeth Salander defines trust as a calculated system of boundaries, verification, and leverage rather than a subjective emotional state. By treating connection as a security protocol, she utilizes strict access rules and constant reliability testing to mitigate the risks of betrayal inherent in interpersonal relationships and predatory institutional structures.
Why does Lisbeth Salander prioritize objective verification over emotional connection?
Lisbeth prioritizes objective verification because repeated institutional betrayal and personal trauma have conditioned her to view vulnerability as a survival risk. Her hyper-vigilance manifests as psychological firewalls, where she gathers extensive intelligence on others and tests their motives forensically before allowing any degree of emotional or physical access.
How does Mikael Blomkvist successfully navigate Lisbeth Salander’s trust protocols?
Mikael Blomkvist navigates Lisbeth’s trust protocols through a sequence of earned permissions and repeatable, transparent behaviors. He proves his reliability by maintaining professional boundaries, respecting her autonomy, and remaining non-exploitative during their investigative collaboration. This iterative proof allows Lisbeth to slowly lower her security firewalls and share sensitive personal data.
What boundary-setting techniques characterize Lisbeth Salander’s psychological approach?
Lisbeth Salander’s psychological approach involves controlling the flow of personal information, escalating access slowly based on proven behavior, and utilizing verification before making commitments. These principles focus on treating safety as a measurable pattern of consistent actions rather than an intuition, emphasizing clear personal limits and the documentation of agreements.
What role does leverage play in Lisbeth Salander’s interpersonal security?
Leverage serves as a critical safeguard in Lisbeth’s trust system, ensuring she is never completely vulnerable to those she permits into her inner circle. By maintaining specialized technical skills and gathering defensive data, she creates a power balance that discourages exploitation, allowing her to function within a world she perceives as predatory.
Further Reading & Authoritative Sources
Authoritative Sources
- ‘Girl with the Dragon Tattoo’ Review: Grisly, Unne — A review from a reputable news magazine that closely analyzes David Fincher’s 2011 adaptation and comments extensively on Rooney Mara’s interpretation of Lisbeth Salander as a character.